Other
The "Other" REDDOXX Cloud Tenant is used when there is no M365 instance.
This is the case, for example, in on-premises environments where emails are stored on a local E-Mail Server and users and login credentials are managed in a directory service.
In this scenario, the REDDOXX Cloud Connector is required.
For the connection between REDDOXX Cloud Tenant and a local directory service you need:
- access to the public DNS configuration of your domain to be connected
- the REDDOXX Cloud Connector
- a read-authorised account to your directory
- a Windows system on which the REDDOXX Cloud Connector can be installed
- use the link https://admin.cloud.reddoxx.com and click on "Create new tenant"
- select "Other" to create a tenant that is to be set up for an OnPremise environment. Click on "Continue"
- enter an email address associated with your OnPremise environment for registration
You will then receive a confirmation email and a DNS TXT record that must be stored in your DNS for the domain to be registered
Then click on the link in the email to finalise the setup - assign a secure password and specify the name of the tenant
- click on Create tenant
If you already know inclusion or exclusion criteria for archiving, you can create these under Email Archive => Policies.
The rules are processed in the visible order. The first rule that matches is applied, all following rules are ignored.
You can move the rules using the ≡ symbol.
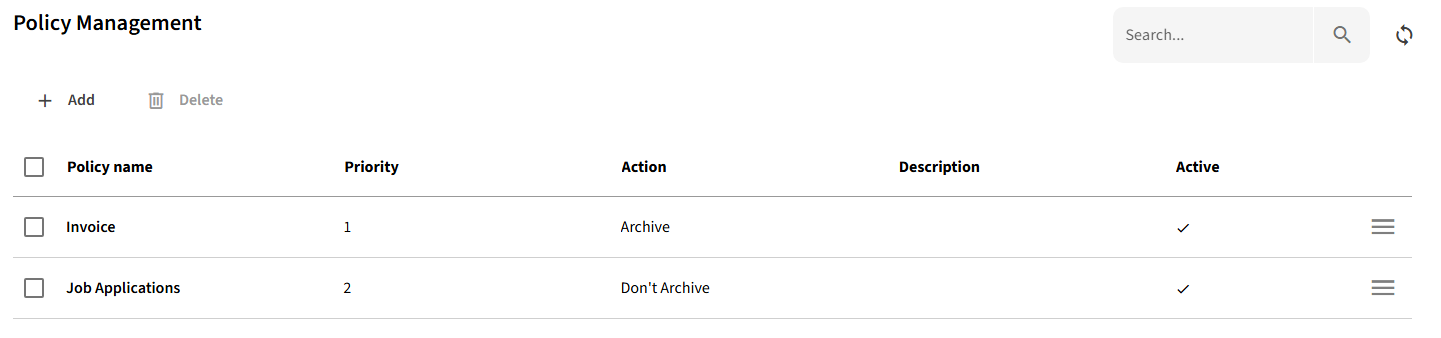
- click on "+ Add"
- provide a name for the rule and set the action (archive / don´t archive)
- specify the criteria in the Subject pattern, Sender pattern, Recipient Patterns and Size Filters tabs. Please note that the criteria are AND-linked.
- "Save" the rule
In the Tenant => Configuration area, you will find the tenant e-mail address that you enter as the target address in the journaling of your e-mail server.
To establish a connection between your on-premises environment and the REDDOXX Cloud tenant, you will need the REDDOXX Cloud Connector.
You install this locally on a Windows system from which the local directory is accessible.
To set up the Cloud Connector, you need to carry out a few steps within the tenant and also within the Connector itself:
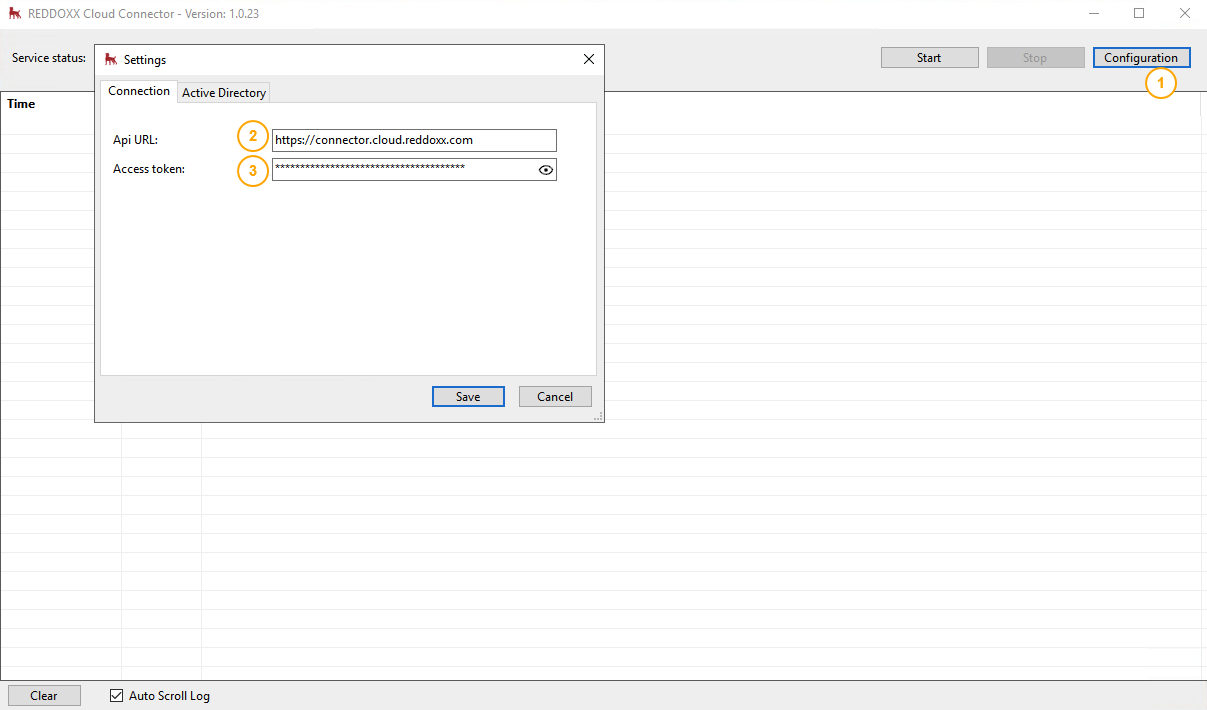
- Launch the Cloud Connector after installation and select ‘Configuration’
- Check that the API URL in the connector is correct (https://connector.cloud.reddoxx.com) and adjust any firewall settings so that the connector can access the interface
- Enter the access token for the Cloud Tenant
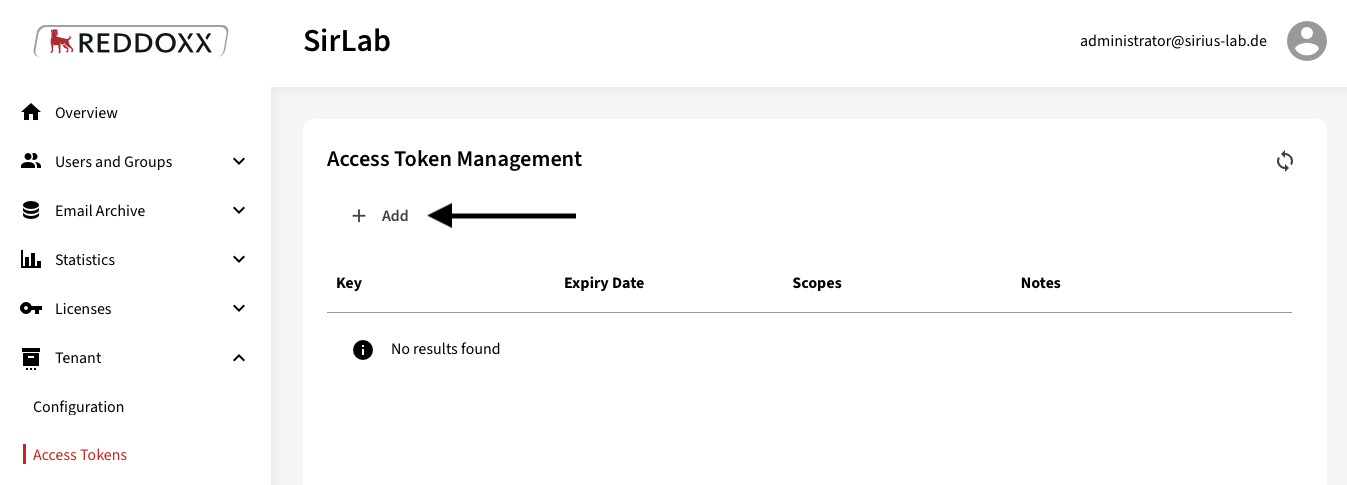
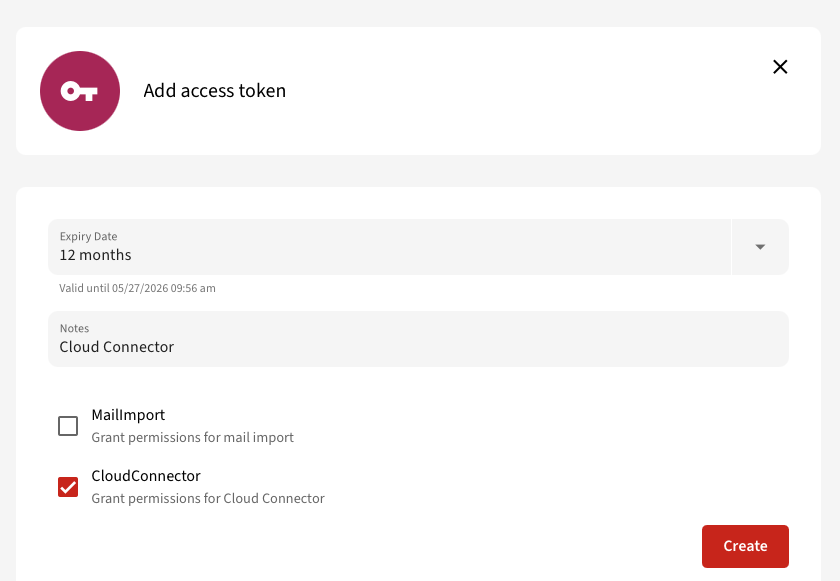
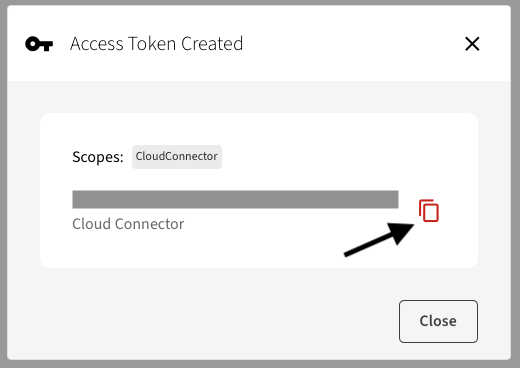
You can create the access token in the REDDOXX Cloud Tenant under Tenant => Create access token
Now switch to the Active Directory tab (1) in the Cloud Connector
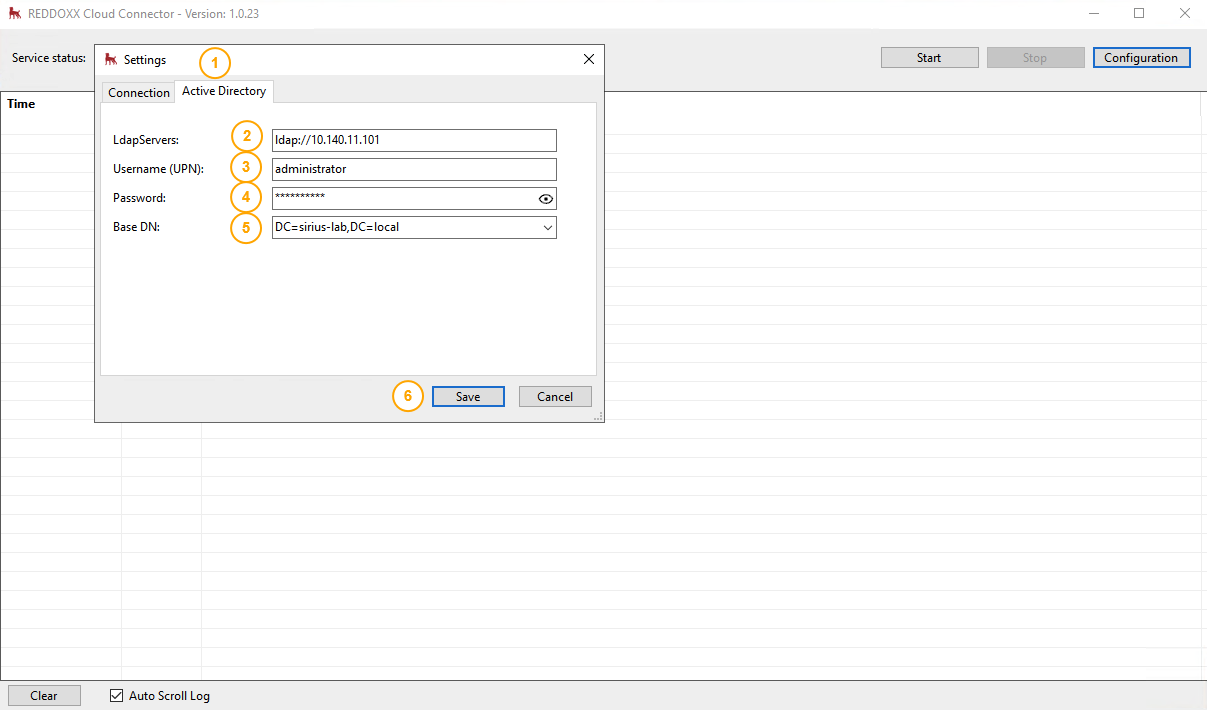
Specify the LDAP server (using ldap:// or ldaps://) and use the correct credentials with a service account that has read permissions.
Then save the settings and let the connector restart the service.
Make sure that the Cloud Connector is running (1)
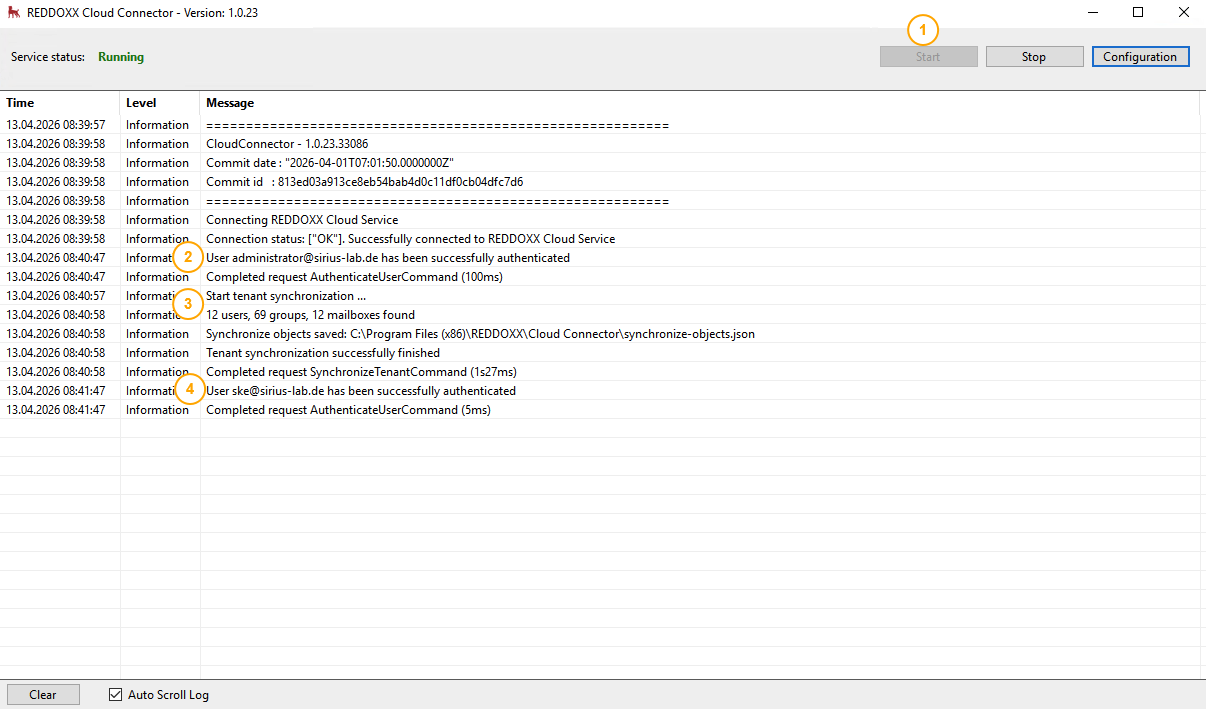
Once the following steps are complete (2, 4), the login details and synchronisation results will also appear here (3)
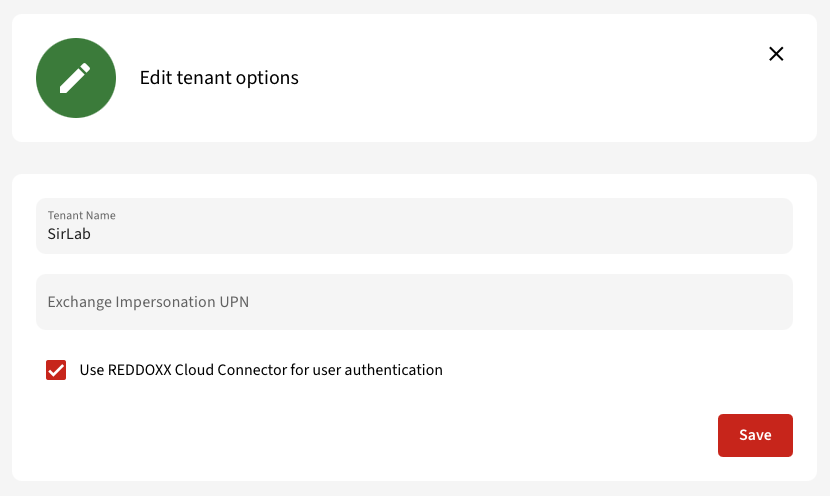
Now go to the settings in the REDDOXX Cloud Tenant and click on the edit icon under Tenant => Configuration:
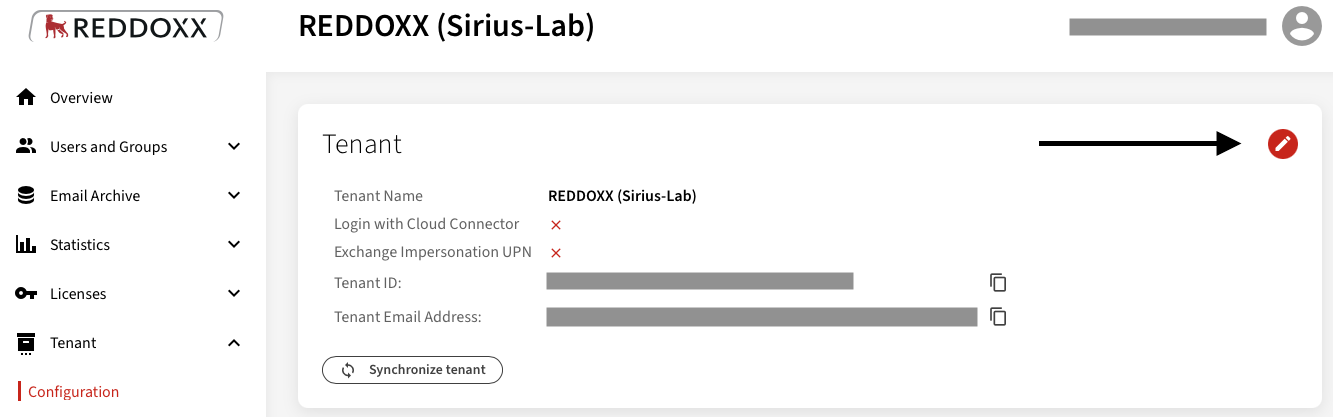
Select "Use REDDOXX Cloud Connector for user authentication" and save the settings:
You can now synchronise the tenant with the REDDOXX Cloud Connector:
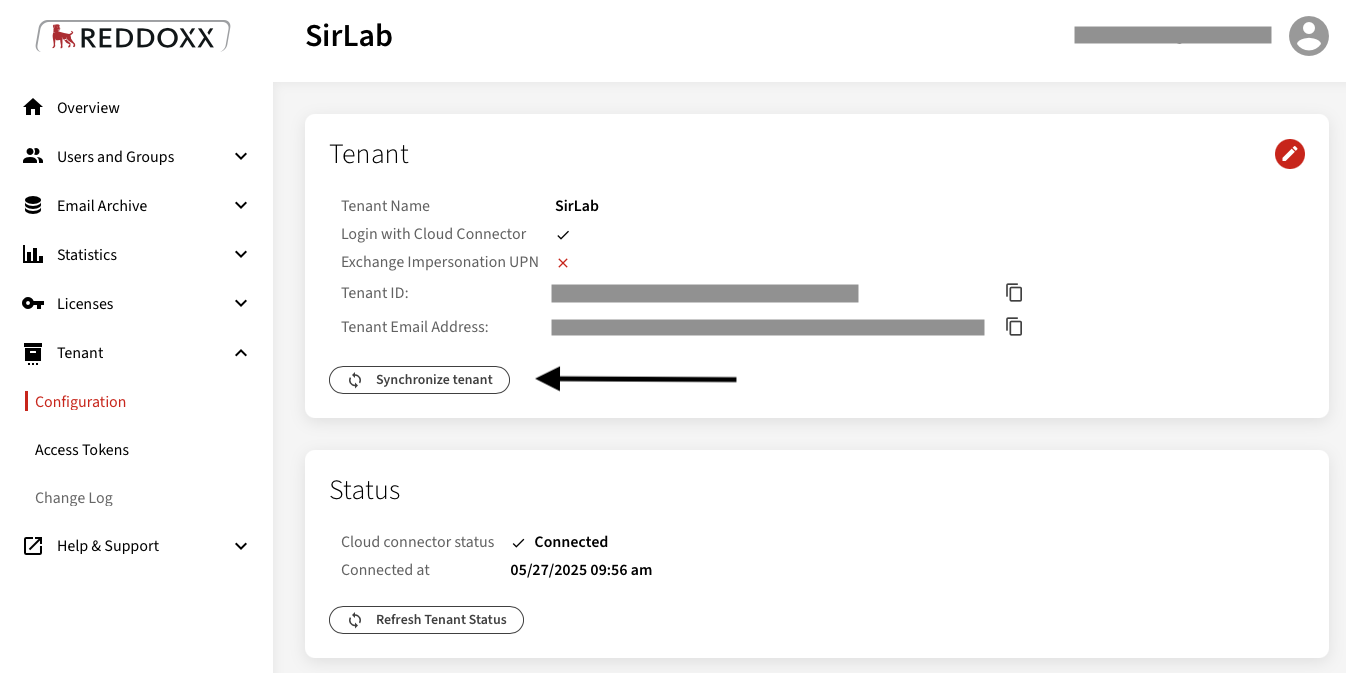
Please note: If the Cloud Connector is used for login, the tenant admin will also have to log in with the AD credentials in future.